Applied Interpretability: Foundation-Sec-Instruct Goes Under the Microscope
Exploring mechanistic interpretability methods for understanding internal behavior of security-focused language models.
Exploring mechanistic interpretability methods for understanding internal behavior of security-focused language models.
A framework for transforming traditional detection engineering logic into LLM-driven reasoning systems.
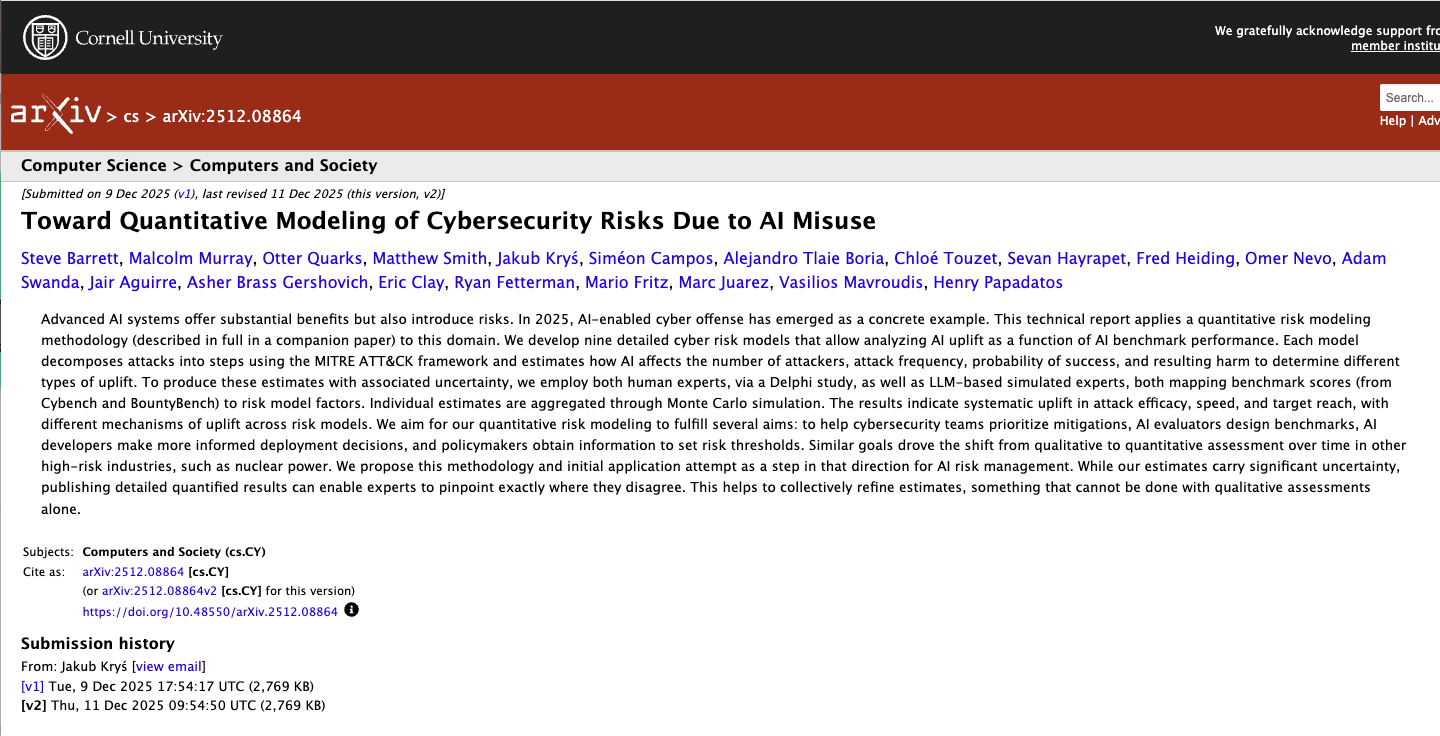
A framework for estimating cyber risk introduced by malicious and unintended AI use patterns.

Hands-on guide for modern threat hunting workflows with practical methods and queries.

A structured framework for model-assisted and evidence-driven threat hunting workflows.

Presentation materials for Defending at Machine Speed, focused on practical use of security context to improve AI-assisted detection and response workflows.

YouTube appearance focused on methods and use cases from The Threat Hunter's Cookbook.

Video appearance covering AI-enabled adversary trends and emerging malware behavior.

YouTube discussion of annual Macro-ATT&CK findings and defender takeaways.

YouTube appearance discussing threat-informed planning and macro-level ATT&CK trend analysis.

By analyzing new domain registrations around major real-world events, researchers show how fraud campaigns take shape early, helping defenders spot threats before scams surface.

The security experts on the SURGe team have released The Threat Hunter’s Cookbook, a hands-on guide for security practitioners that features actionable insights into threat hunting methods, ready-to-use queries, and more.

Enhance LLM performance for cybersecurity tasks with few-shot learning, RAG, & fine-tuning guide models for accurate PowerShell classification.

Splunker Ryan Fetterman explains how Splunk DSDL 5.2 enhances cybersecurity operations, streamlining PowerShell script classification and reducing analyst workload by 250x.

Explore the impact of autonomous adversaries on cybersecurity as AI and LLMs evolve.

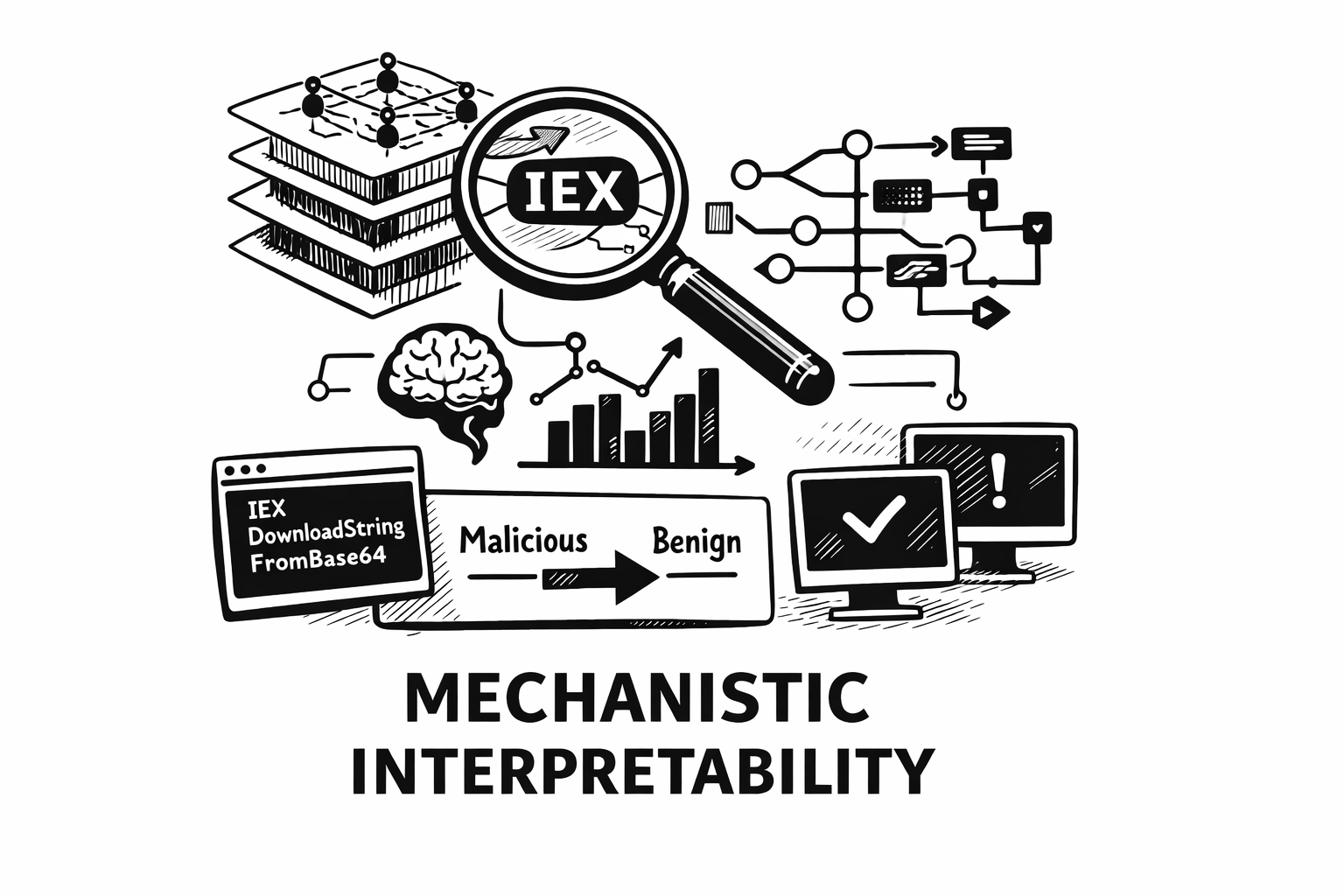
Splunk's Mick Baccio and Ryan Fetterman explore 2024's macro-level cyber incident trends through the lens of the MITRE ATT&CK framework.

Splunk’s Ryan Fetterman and Tamara Chacon dive into attacker techniques, trends, and blue team tips for analyzing and visualizing data from the past year.

SURGe experiments with a method to find masquerading using M-ATH with Splunk and the DSDL App.

SURGe reviews the latest attacker trends and behaviors with this look at four years of ATT&CK data from some of the largest and most trusted threat reporting sources.

Explore applied model-assisted threat hunting for dictionary-based domain generation algorithms using the SURGe Security Research Team's PEAK Threat Hunting Framework.

Welcome to the third entry in our introduction to the PEAK Threat Hunting Framework! Taking our detective theme to the next level, imagine a tough case where you need to call in a specialized investigator. For these unique cases, we can use algorithmically-driven approaches called Model-Assisted Threat Hunting (M-ATH).

As AI / Machine Learning (ML) systems now support millions of daily users, has our understanding of the relevant security risks kept pace with this wild rate of adoption?

Aggregated analysis of global ATT&CK-mapped threat reporting